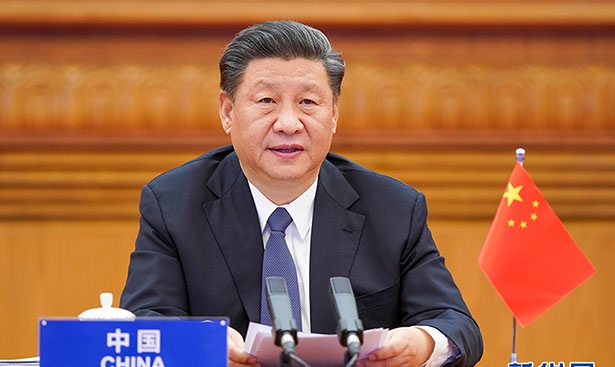
BlackBerry Ltd. has come up with a sensational report that indicates that Chinese state-sponsored hackers have been stealing data from computers across the globe for almost around a decade. A significant reason for this unnoticed attack is its target, Linux operating systems.
Blackberry claims a new 44-page long report. It claims advanced hackers from China camouflaged their software tools posing a low-level security risk in the form of advertisements. The approach made it possible for them to extract information out of their targeted systems.
With low-level security tools affecting a limited number of systems, the hackers were able to work in the shadows for almost eight years. The tools used by the hackers were not new. Still, they were aptly targeted on Linux systems to escape the scrutiny of most of the cybersecurity experts working on either Microsoft Windows or Google Android.
A total of five different advanced persistent threat (APT) groups found to be responsible for the attacks, all of which claimed to be state-sponsored in one way or another. The report, however, clarifies that this involvement can be denied by the Chinese government due to the nature of the attacks carried out.
Why Linux?
Linux is not the optimum choice of an operating system for regular use and hence its use has been limited to less than 2% of the entire world’s desktop usage. That said, Linux does occupy a premium position in the computing world, powering all of the top 500 supercomputers in the world.
With such an apex position and almost no attention to cybersecurity entities, Linux proved to be an ideal target for the Chinese APT groups. Actively deployed since March 13, 2012, the hacking is considering to be “highly probable” to have impacted a significant number of organizations and that “the duration of the infections lengthy.”
The scale of the attack is still just an estimate. Still, given the type of information mostly present in a top-grade Linux system as well as the duration of the attack, it is probable that the Chinese government was able to extract many valuable data through the malpractice.
As BlackBerry mentions it in the report, “these [APT] groups have readily adapted, shared new tools, borrowed from open-source resources, and developed new methods to harvest information – all while effectively hiding more or less in plain sight.”




![[HINDI] What is DoS attack and DDoS attack?](https://bittentechsolutions.in/wp-content/uploads/2020/04/ddos-218x150.jpg)
![[HINDI] What is juice jacking? Think twice before using public USB ports](https://bittentechsolutions.in/wp-content/uploads/2020/04/juice-jacking-risk-1200x675-1-218x150.jpg)