The U.S. Branch of Justice (DoJ) yesterday uncovered charges against two Chinese nationals for their supposed association in 10 years in length hacking binge focusing on dissenters, government offices, and several associations in upwards of 11 nations.
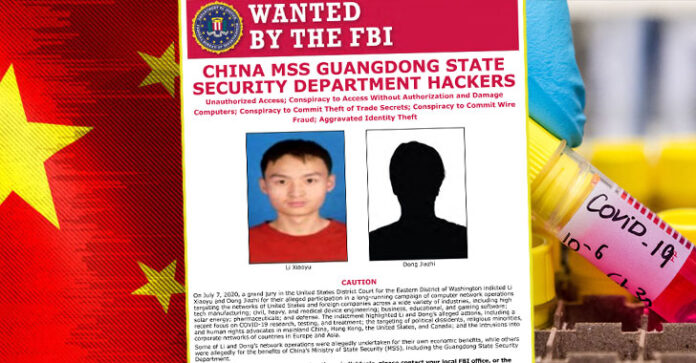
The 11-check arraignment, which was unlocked on Tuesday, charges LI Xiaoyu (李啸宇) and DONG Jiazhi (董家志) took terabytes of delicate information, including from organizations creating COVID-19 immunizations, testing innovation, and medicines while working both for private monetary profit and benefit of China’s Ministry of State Security.
“China has now had its spot, close by Russia, Iran and North Korea, in that dishonorable club of countries that give a place of refuge to digital crooks in return for those hoodlums being ‘accessible if the need arises’ to work to serve the state, [and] to take care of the Chinese Communist gathering’s unquenchable crave American and other non-Chinese organizations’ well deserved protected innovation, including COVID-19 exploration,” said Assistant Attorney General John C. Demers, who drives the DoJ’s National Security Division.
The pair, who are presently needed by the U.S. Government Bureau of Investigation, went under the radar after they bargained a U.S. Division of Energy organize in Hanford, which is home to a decommissioned atomic creation complex situated in the territory of Washington.
Beside this penetrate, the people in questions have been blamed for invading the systems of organizations spreading over innovative assembling, modern designing, barrier, instructive, gaming programming, and pharmaceutical divisions with a mean to take proprietary advantages and other secret business data.
Other than the U.S., various casualty associations are situated in Australia, Belgium, Germany, Japan, Lithuania, the Netherlands, Spain, South Korea, Sweden, and the U.K. On the whole, the focused on cyberattacks kept going over a time of over ten years, beginning around September 1, 2009, and proceeding through July 7, 2020, the DoJ said.
Misusing Unpatched Vulnerabilities in Web Applications
As indicated by the arraignment, the programmers increased an underlying traction to the organizations by misusing shaky default arrangements or newly uncovered security blemishes in famous programming that hadn’t yet been fixed.
The two suspects, at that point, introduced qualification taking programming to increase further access and utilized web shells to execute malevolent projects, and move the information as packed RAR records, yet not before changing their expansions to “.JPG” to cover the exfiltration procedure as harmless pictures.
The taken information, which ran into several gigabytes, comprised of source code, data about medications under dynamic turn of events, weapon plans, and actually recognizable data, the DoJ noted.
Likewise, all the malignant exercises were performed on the Recycle Bin of the focused on Windows frameworks, utilizing it to stack the executables into explicit organizers and spare the RAR documents.
“In at any rate one case, the programmers looked to blackmail digital currency from a casualty substance, by taking steps to discharge the casualty’s taken source code on the Internet,” the DoJ said. “All the more as of late, the litigants examined for vulnerabilities in PC systems of organizations creating COVID-19 immunizations, testing innovation, and medicines.”
It’s Not Just China
The advancement is even more huge since it comes only months after both the FBI and Homeland Security cautioned that China was effectively attempting to take information from associations dealing with COVID-19 exploration and in the midst of mounting strains between the U.S. what’s more, China over national security concerns.
Yet, China isn’t the main country that has been blamed for utilizing its hostile digital capacities to take coronavirus research.
In May, Iran-supported programmers purportedly focused on U.S. drugmaker Gilead, whose antiviral medication remdesivir has been demonstrated to trigger a safe reaction in patients tainted with COVID-19.
At that point a week ago, the U.K’s. National Cyber Security Center (NCSC) asserted that programmers connected to Russian insight administrations (APT29 or CozyBear) had focused on organizations exploring a coronavirus antibody in the U.S., U.K., and Canada without indicating which associations had been focused on, or whether any data had been taken. Russia has denied the charges.
Li and Dong are accused of wholesale fraud, intrigue to submit wire misrepresentation, burglary of proprietary advantages, and disregarding against hacking laws, all of which by and large convey a most extreme sentence of more than 40 years.




![[HINDI] What is DoS attack and DDoS attack?](https://bittentechsolutions.in/wp-content/uploads/2020/04/ddos-218x150.jpg)
![[HINDI] What is juice jacking? Think twice before using public USB ports](https://bittentechsolutions.in/wp-content/uploads/2020/04/juice-jacking-risk-1200x675-1-218x150.jpg)